Access Control Policy Enforcement For Zero-Trust-Networking .abstract—the evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and. A policy enforcement framework to address many of open.
from www.aiophotoz.com
A policy enforcement framework to address many of open.abstract—the evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and.
Forrester Zero Trust Model Images and Photos finder
Access Control Policy Enforcement For Zero-Trust-Networking A policy enforcement framework to address many of open.abstract—the evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and. A policy enforcement framework to address many of open.
From www.serenoclouds.com
Microsoft Zero Trust Security Sereno Cloud Solution Access Control Policy Enforcement For Zero-Trust-Networkingabstract—the evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and. A policy enforcement framework to address many of open. Access Control Policy Enforcement For Zero-Trust-Networking.
From www.tech-exclusive.com
Implementing Zero Trust Network Access Control Best Practices Tech Access Control Policy Enforcement For Zero-Trust-Networking A policy enforcement framework to address many of open.abstract—the evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and. Access Control Policy Enforcement For Zero-Trust-Networking.
From www.xorlogics.com
6 Tips for Implementing Access Control Authentication System With Access Control Policy Enforcement For Zero-Trust-Networkingabstract—the evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and. A policy enforcement framework to address many of open. Access Control Policy Enforcement For Zero-Trust-Networking.
From www.threatshub.org
Modernize secure access for your onpremises resources with Zero Trust Access Control Policy Enforcement For Zero-Trust-Networkingabstract—the evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and. A policy enforcement framework to address many of open. Access Control Policy Enforcement For Zero-Trust-Networking.
From cybertechaccord.org
Zero Trust Access Policies Policy Based Adaptive Access Access Control Policy Enforcement For Zero-Trust-Networking A policy enforcement framework to address many of open.abstract—the evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and. Access Control Policy Enforcement For Zero-Trust-Networking.
From blogs.arubanetworks.com
Protecting the organization with Zero Trust network security Aruba Blogs Access Control Policy Enforcement For Zero-Trust-Networkingabstract—the evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and. A policy enforcement framework to address many of open. Access Control Policy Enforcement For Zero-Trust-Networking.
From awestruckking.blogspot.com
zero trust network access Awestruck King Access Control Policy Enforcement For Zero-Trust-Networkingabstract—the evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and. A policy enforcement framework to address many of open. Access Control Policy Enforcement For Zero-Trust-Networking.
From www.f5.com
Zero Trust in an ApplicationCentric World Access Control Policy Enforcement For Zero-Trust-Networking A policy enforcement framework to address many of open.abstract—the evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and. Access Control Policy Enforcement For Zero-Trust-Networking.
From learn.microsoft.com
Securing identity with Zero Trust Microsoft Learn Access Control Policy Enforcement For Zero-Trust-Networking A policy enforcement framework to address many of open.abstract—the evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and. Access Control Policy Enforcement For Zero-Trust-Networking.
From learn.microsoft.com
Zerotrust security guide for Microsoft Teams Use Teams securely on Access Control Policy Enforcement For Zero-Trust-Networkingabstract—the evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and. A policy enforcement framework to address many of open. Access Control Policy Enforcement For Zero-Trust-Networking.
From braxtongrant.com
Initiating your Zero Trust Security Framework BG Technologies Blog Access Control Policy Enforcement For Zero-Trust-Networking A policy enforcement framework to address many of open.abstract—the evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and. Access Control Policy Enforcement For Zero-Trust-Networking.
From student-activity.binus.ac.id
Zero Trust Security Framework Cyber Access Control Policy Enforcement For Zero-Trust-Networkingabstract—the evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and. A policy enforcement framework to address many of open. Access Control Policy Enforcement For Zero-Trust-Networking.
From www.researchgate.net
(PDF) Access Control Policy Enforcement for Access Control Policy Enforcement For Zero-Trust-Networkingabstract—the evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and. A policy enforcement framework to address many of open. Access Control Policy Enforcement For Zero-Trust-Networking.
From www.techtarget.com
What is zerotrust network access? ZTNA basics explained TechTarget Access Control Policy Enforcement For Zero-Trust-Networking A policy enforcement framework to address many of open.abstract—the evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and. Access Control Policy Enforcement For Zero-Trust-Networking.
From www.spiceworks.com
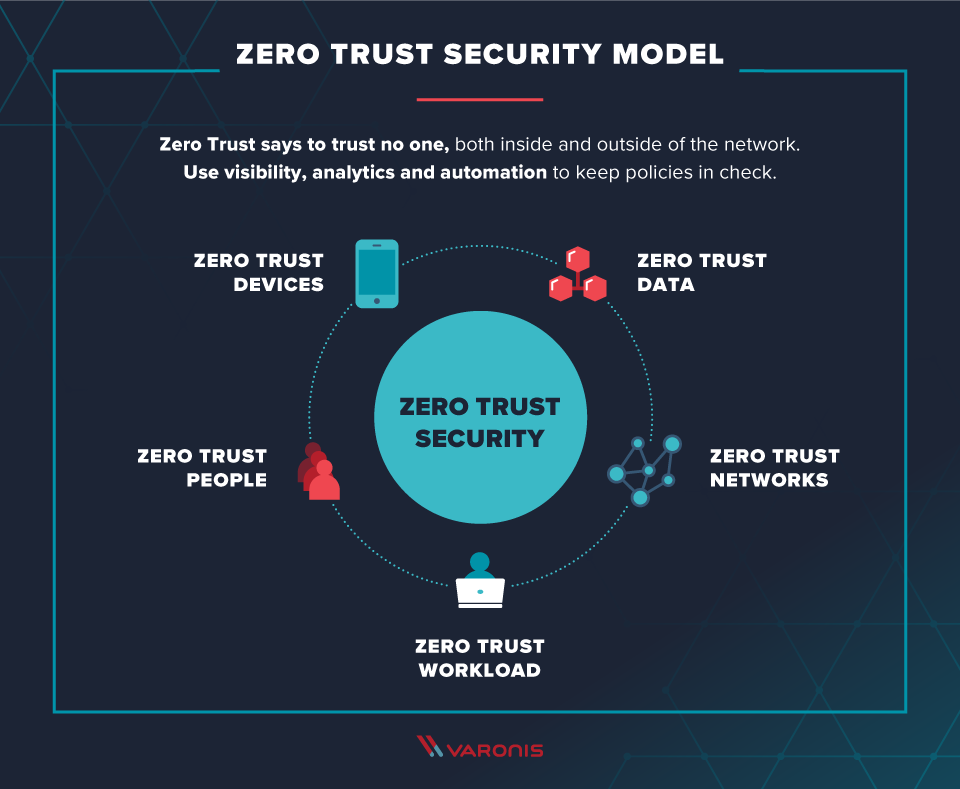
What Is Zero Trust Security? Definition, Model, Framework and Vendors Access Control Policy Enforcement For Zero-Trust-Networking A policy enforcement framework to address many of open.abstract—the evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and. Access Control Policy Enforcement For Zero-Trust-Networking.
From duo.com
The Zero Trust Approach to Important Control Planes Duo Security Access Control Policy Enforcement For Zero-Trust-Networking A policy enforcement framework to address many of open.abstract—the evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and. Access Control Policy Enforcement For Zero-Trust-Networking.
From www.coreview.com
What is Zero Trust Security? Access Control Policy Enforcement For Zero-Trust-Networking A policy enforcement framework to address many of open.abstract—the evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and. Access Control Policy Enforcement For Zero-Trust-Networking.
From www.zscaler.fr
Zero Trust and its Role in Securing the New Normal Zscaler Access Control Policy Enforcement For Zero-Trust-Networkingabstract—the evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and. A policy enforcement framework to address many of open. Access Control Policy Enforcement For Zero-Trust-Networking.